What is SASE or Secure Access Service Edge ?
Is it SD-WAN? Is it something related to security? Everyone talks about SASE, very few are clear on the concept and its positioning versus SD-WAN and Security.
The jargon out there in the literature is enough to confuse many.
I will try to make it easy for you to understand if you follow along. In the end, you will know and appreciate SASE, its benefit and understand exactly the “SASE and SD-WAN difference“
When Gartner used this term for the first time in 2019, many took it for granted. Some ruled it out as having something that could impact the networking industry.
Today SASE has got enough traction with many vendors rolling out solutions under SASE.
What is SASE? Definitions
Gartner defines SASE as
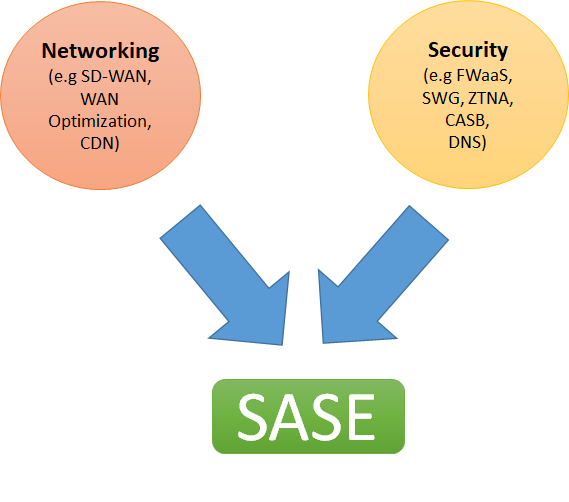
“The secure access service edge is an emerging offering combining comprehensive WAN capabilities with comprehensive network security functions (such as SWG, CASB, FWaaS, and ZTNA) to support the dynamic secure access needs of digital enterprises”
In simple words by Gartner, SASE is a combination of networking and Security.
And as described in simple words by a blog at Gartner here
“SASE combines network security functions (such as SWG ie. Secure Web Gateway, CASB, FWaaS, and ZTNA), with WAN capabilities (i.e., SDWAN) to support the dynamic secure access needs of organizations. These capabilities are delivered primarily aaS and based upon the identity of the entity, real-time context, and security/compliance policies”
However, I like the MEF definition as it is more simple
“A service connecting users (machine or human) with their applications in the cloud while providing connectivity performance and security assurance determined by policies set by the Subscriber.”
What Problem SASE is trying to solve?
As enterprises transition to digital transformation, more and more applications are moving to the cloud. Applications, no longer reside on-premises or in the data centers and more and more workforce is becoming remote and mobile, the cloud and mobility both present challenges to enterprises.
For example, if the data center is no longer the center of applications? Would it make sense to have all connectivity routed through the data centers for security checks as traditional connectivity would demand?
When applications are sprawled all over the cloud, what would be the best way to connect users with applications.
Yes SD-WAN does solve the problem of connectivity by offering users a way to connect to clouds directly bypassing HQ in many cases. However, it is only half the story.
It is easier said than done! How?
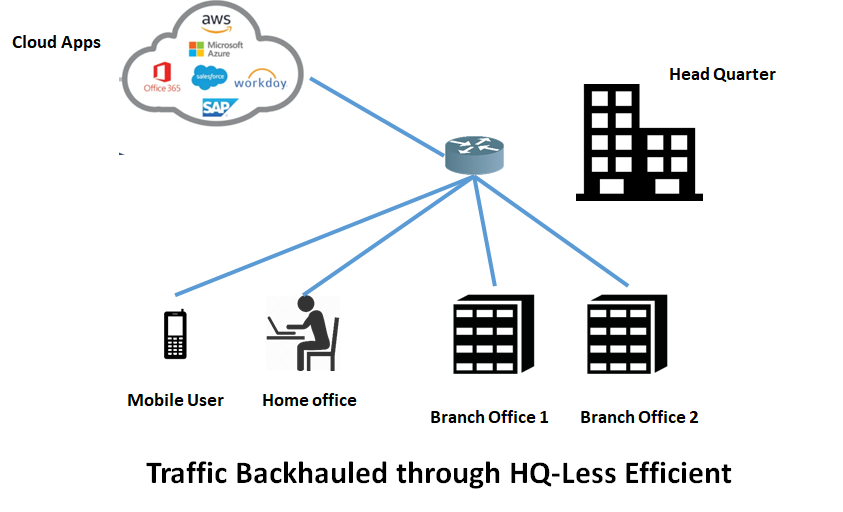
It would call for additional security checks most likely at the branch office, itself. Shifting the security nucleus from HQ to the branch offices is not a scalable solution.
Adding more security appliances ( NGFW, IPS, IDS) at the branch offices is both CAPEX and OPEX intensive. It makes the job of the IT team complex to maintain and troubleshoot.
Could there be a better way?
Welcome to the world of SASE!
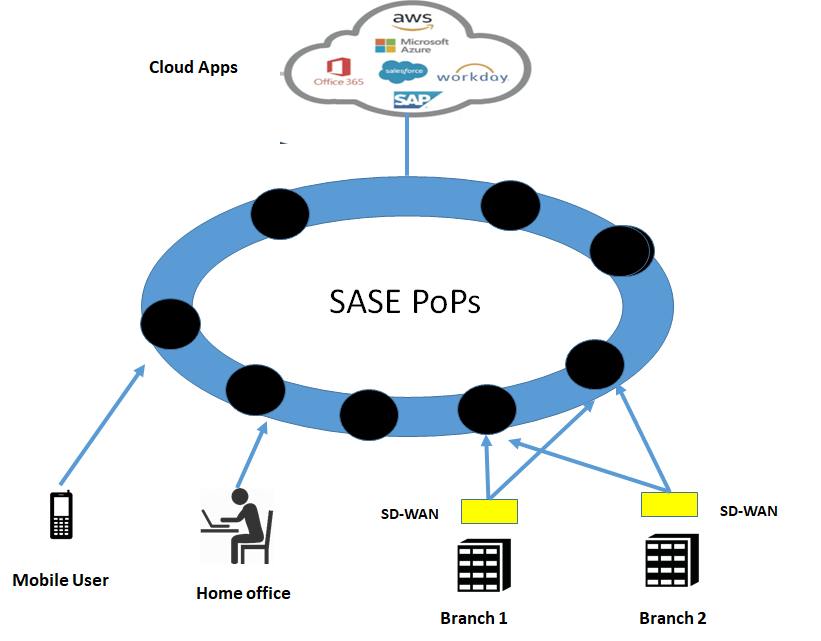
SASE offers a way for enterprises to connect to the clouds directly in a secure way without having advanced security appliances on-site, Security is offered by the cloud itself. The SASE provider would offer its PoP closer to the users offering all advanced features as a service for NGFW, CASB, SWG.
SASE Architecture /SASE Cloud
With SASE latency matter for the applications, The SASE solution, therefore, offers distributed PoPs with some closer to the users to optimize the latency and user experience. SASE will act as a gateway routing the traffic through SASE gateways to the applications elsewhere in the cloud.
The architecture of SASE is based on cloud-native principles. A cloud-native architecture enables agility, elasticity and adaptability
SASE cloud is implemented as a distributed cloud platform. Wherever the edges are, the networking and security features should be available to provide low latency PoP for services.
SASE providers will establish SASE PoPs closer to the users to provide them access to the application.This will enable edge SD-WAN devices to access applications through the cloud that has Firewall as a service, Secure Web Gateway, Advanced Threat protection, all in one cloud.
Is SASE only security offering through clouds?
No!
Security has always been offered by security vendors as a service in clouds. Zscaler and Palo Alto have been offering such solutions for quite some time.
There is nothing new here.
What is offered now is an integrated connectivity/SD-WAN offering mixed with the security offering as one solution by ONE VENDOR.
Hold on! But SD-WAN has security functions too? What is the difference between SD-WAN and SASE then?
Now before you come back asking, well SD-WAN already has security functions built-in or they can be added as service chaining on demand, what is new with SASE, then?
Let me explain.
As I already explained, SD-WAN strength is “connectivity” and not security. Security was brought in as a feature to help the branch offer secure access without the need for going to HQ.
While this is a workable solution. It is not the most efficient one.
It needs a built-up of security appliances at the branch office itself, which is complex and costly. But more importantly, it does not solve the problem of the mobile workforce ( perhaps individuals) that want to connect remotely to applications for example from another country. That sort of traffic would still need to be brought for security checks at the HQ. Which creates additional latency and longer paths.
To understand the concept. Consider the following diagram, SD-WAN provides connectivity and security functions at a branch office, however, after transitioning to SASE, the only function needed at the branch office is the SD-WAN router, while all security functions are moved to the SASE cloud.
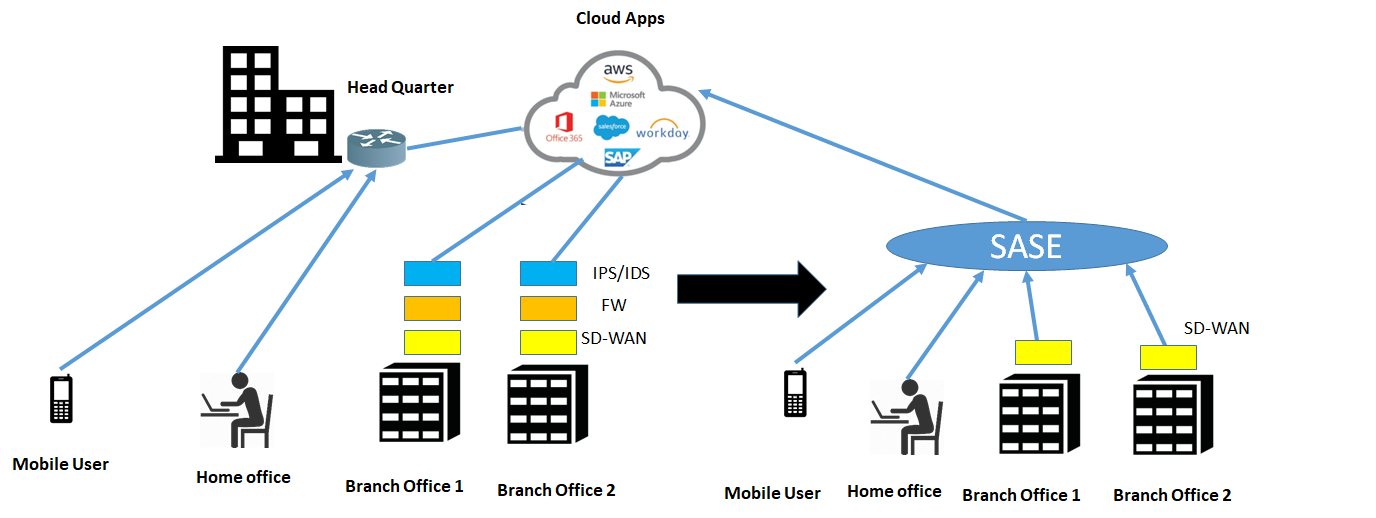
SASE says that if resources move to the cloud, the most efficient way to build connectivity is to have direct access to the clouds and hence it makes sense to have security checkpoints in the cloud themselves. That is bringing inspection points close to the applications themselves.
Therefore SASE is a convergence of networking ( such as SD-WAN) and network security services ( such as SWG, CASB, and FWaaS, multi endpoint protection). with the added benefit of a centralized management plane enabling a single pane of glass.
Heavy Branch to Cloud-centric Thin branch/SASE models
Naturally, when major functions move to the cloud, the only thing left at branch office is a simple SD-WAN box that provides connectivity to the cloud. This is called “Thin Branch” and heavy cloud model
At the site besides SD-WAN, there could be other network functions such as WAN optimization, traffic analysis functionality, etc.

Identity Driven
One of the important concepts in SASE is that it is Identity driven.
Identity is the most important element in SASE. Every user in SASE has identity, a person, an application service or a device.
Examples of user identity include such as
Name of a person
MAC address of the laptop
Identifier of IOT Device
The second important item is the context, which includes
Location
Time of the Day
level of assurance ( NIST, X 509 Certificates, etc)
With SASE both are important, Identity when attached with the context can provide a dynamic set of security policies that can change as the context changes. This enables a very powerful and rich set of security policies that can be applied to the users of the SASE Cloud.
Benefits of SASE
User Experience
The first and foremost benefit of SASE is the enhanced user experience because of the shorter reach to the destination. Almost all traffic that was supposed to go to the HQ can now be sent to the nearest SASE PoP thus reducing latency and enhancing user experience.
Cost reduction
Costs are reduced as SASE eliminates the need for point solutions. Everything is integrated in a single cloud with some networking part at the customer site. The box at customer sites is simplified to the extent,, that it needs just SD-WAN connectivity up to the nearest PoP of SASE. All the heavyweight processing occurs in the cloud. OPEX is reduced as IT teams need to maintain a converged network and security stack managing all features and policies from a single interface
Mobility
The biggest advantage for the SASE for business is enabling mobility of the users. With the world changing to the mobile workforce, remote users ( some workforce from can connect to their enterprise/business cloud or application clouds from anywhere in the world without worrying about the security and without the need to dial in their corporate VPNs. Also home has become the office for the workforce today. All they have to do is to connect to the nearest PoP of the SASE provider. SASE simplifies the authentication process by applying appropriate policies for the relevant resources which a user seeks.
Less Complexity, Less Integration
With preferably one provider for SD-WAN and security, there will be no need for complex integrations because of service chains. Having multiple security vendors/functions in a service chain requires a lot of integration which results in delays to provide service and CAPEX spending
So that’s it an introduction about SASE ( Secure Access Service Edge and I hope it is clear now on “what is sase ?”. Go ahead and comment below on what do you think as the future of the SASE.
One final word. SASE is still not part of the Gartner magic quadrant but I expect that it will become sooner or later considering the market traction for SASE

Thanks, Faisal for yet another simple explanation of a new buzzword. Reminds me of “The 3rd Network” (NaaS) MEF was talking about sometime back.
Hi Anuradha, Thanks correct ! Yes SASE is catching up to the hype very quickly…
Very good explanation Faisal.
Still a new concept for many like me.
Thanks a lot Asad ! keep coming back…more to come
Very good piece !
Thanks for visiting Malik
‘With the world changing to the mobile workforce, remote users ( some workforce from can connect to their enterprise/business cloud or application clouds from anywhere in the world without worrying about the security and without the need to dial in their corporate VPNs.’
sums up SASE in 1 sentence
one of the best articles i have seen about SASE, thanks
Thanks Alan for sharing your thoughts, highly appreciated.
Just discovered your blog, and you are doing an amazing job Faisal. Keep going…
Thanks for the encouraging words, keep coming back